Browser Access vs
WP Admin Back End
Access Details
When working with client sites AWESEM tend to have two sites under the client’s installation: the live site (the site that the public views) and a staging site (a private copy of the live site where new functionality and site changes are tested before going live).
Particularly when working with staging sites users may notice there are two sets of access details so the below guide lays out the difference between the WP admin back end access and the browser access.
Particularly when working with staging sites users may notice there are two sets of access details so the below guide lays out the difference between the WP admin back end access and the browser access.
Browser Access Details
Browser access details allow users to view the front end of websites that are essentially password protected. These access details are usually set up for staging or ‘in progress’ sites, where we would not want the general public or search engines to be able to view them but it is helpful for clients to be able to log in to check progress and test elements of the site.
These details do not allow users access to the back end of the site and allow users to view the site only, not make any changes.
They are displayed as a pop up within the browser window and the site will not become visible until the correct details have been displayed, as below:
They are displayed as a pop up within the browser window and the site will not become visible until the correct details have been displayed, as below:
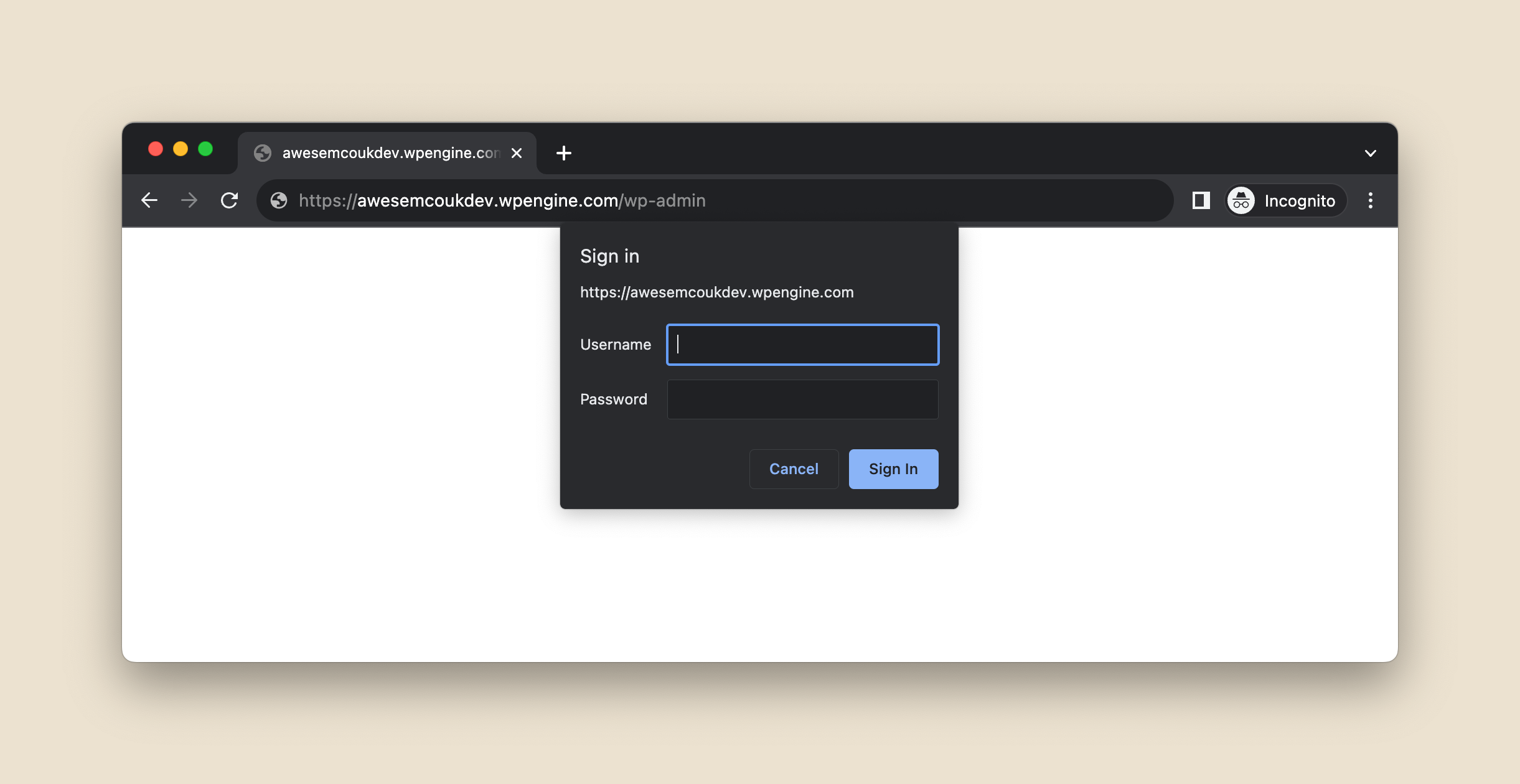
Once these details have been correctly inputted users will then be able to view the front end of the website.
However, to access the back end of the website to make changes or add new content, users will need to log in using the WP admin back end details.
However, to access the back end of the website to make changes or add new content, users will need to log in using the WP admin back end details.
WP Admin Back End Details
This username and password will grant users access to the back end of the site and allow changes and new content to be added to the site. As this access allows users to make changes, it’s important these details are secure and accounts are only set up to users who need access.
Each user who requires access to the back end will have their own, unique set of back end log in details.
Clients should remember to remove access for users who no longer require it; if their job role changes or they leave the organisation, for example. Two factor authentication is another good way to keep this access secure, so we recommend all sites have this enabled.
To enter the WP admin back end details users will need to visit a specific link to view the log in screen, as below:
Each user who requires access to the back end will have their own, unique set of back end log in details.
Clients should remember to remove access for users who no longer require it; if their job role changes or they leave the organisation, for example. Two factor authentication is another good way to keep this access secure, so we recommend all sites have this enabled.
To enter the WP admin back end details users will need to visit a specific link to view the log in screen, as below:
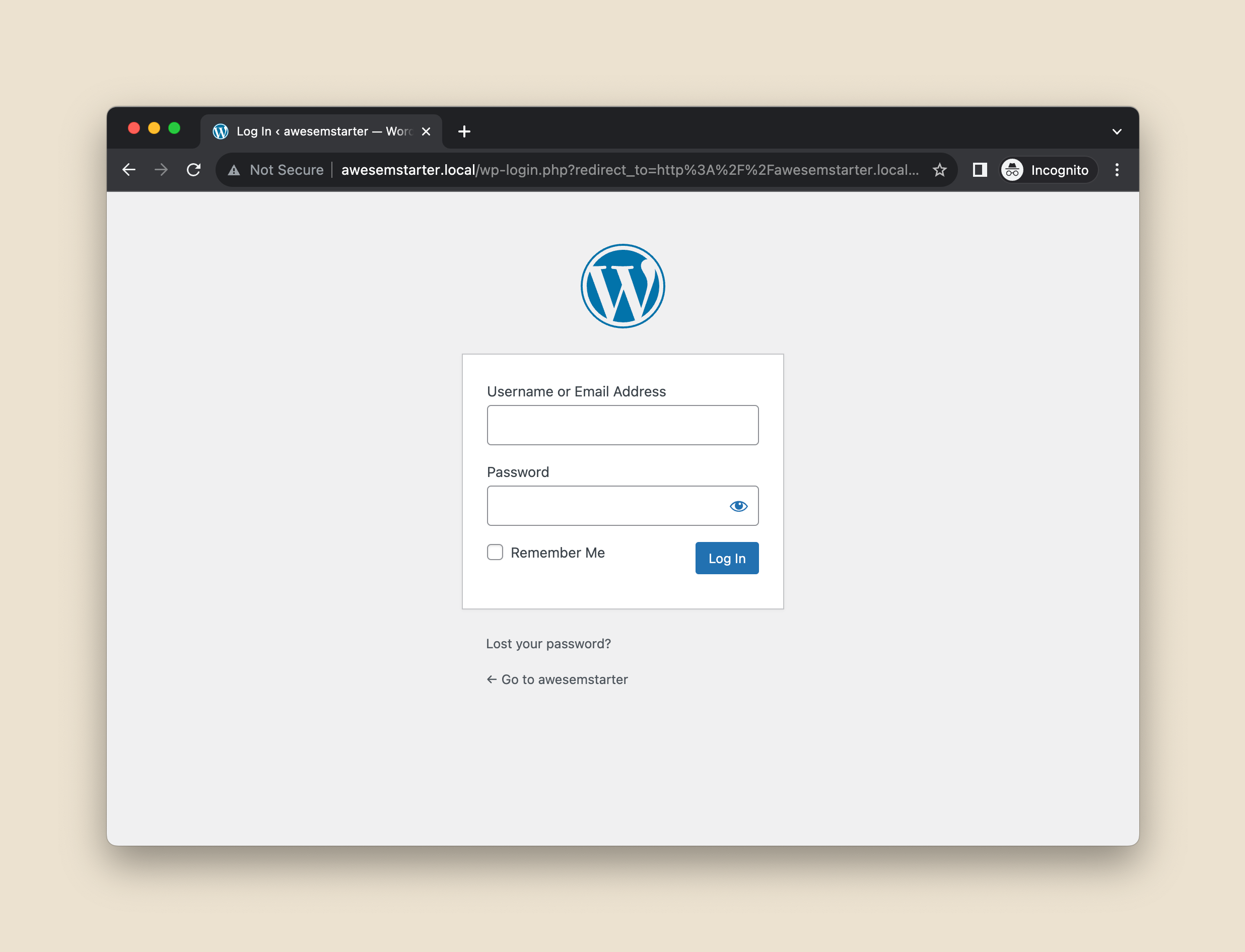
Once these details have been correctly inputted users will be logged into the back end of the site and will be redirected to the WordPress Dashboard.
A few helpful things to note:
A few helpful things to note:
- Browser access allows users to view the front end of the website, back end access allows users to view the back end of the website and make changes to website content.
- Typically there will be one set of browser access details for all users, whereas each individual user should have their own back end access set up.
- Browsers treat the HTTP and HTTPS version of the domain as two different domains and you will have to enter the details twice when you visit the HTTP version first and then get redirected from HTTP to HTTPS.
- Browser access is typically only used on staging sites or pre-launch live sites.
- Live sites typically only require back end access as the front end will be publicly viewable.
- Browser access details and back end details should always be different.
- Back end details should always be secure and unique to each specific log in.
- It’s important to reset back end passwords periodically and ensure they are only stored in a secure, encrypted service.
- We recommend setting up two factor authentication for all back end logins.